The Role of AI in 2026’s Zero-Trust Security Architecture
From "Static Rules" to "Adaptive Intelligence"
The core of Zero Trust has always been "Never Trust, Always Verify." In 2026, however, "verification" is no longer a one-time event at login. AI has transformed ZTA into a Continuous Authentication model.
Instead of a binary "Yes/No" access decision, AI engines now calculate a Dynamic Risk Score in milliseconds. This score changes based on:
Behavioral Biometrics: Is the typing cadence or mouse movement consistent with the user's history?
Environmental Context: Is the request coming from an unusual IP, at an odd hour, or after a suspicious sequence of tool calls?
Device Health: Is the endpoint's security posture currently compromised or unpatched?
3 Pillars of AI-Powered Zero Trust in 2026
1. Identity as the New Micro-Perimeter
In 2026, we don't just secure networks; we secure Identities. This includes both humans and Non-Human Identities (NHIs)—like the AI agents running your CRM or DevOps pipelines.
AI-Curated Governance: AI now manages "Least Privilege" automatically. If an agent hasn't used its "Write" permissions for a week, the AI revokes them, granting them back only via Just-In-Time (JIT) elevation when a specific task requires it.
Composite Identity Tracing: When an agent acts on behalf of a human, AI ensures both identities are verified simultaneously, preventing "Confused Deputy" attacks.
2. Autonomous Microsegmentation
Manually creating firewall rules for thousands of microservices is impossible. AI-driven Microsegmentation now "sees" your network traffic and automatically draws invisible walls around critical data.
Blast Radius Containment: If an AI agent in your marketing department is compromised, the Zero Trust engine detects the anomaly and instantly isolates that agent's network segment before it can move laterally into the finance department.
3. Predictive Threat Containment
Traditional security is reactive; 2026 security is Predictive. Using Generative AI Red Teaming, the Zero Trust architecture constantly "attacks" itself to find weak points in access policies before a real adversary does.
Agent-Level Kill Switches: If an autonomous system starts pulling data 5x faster than normal, the AI doesn't just alert a human—it revokes the agent's credentials instantly across all systems.
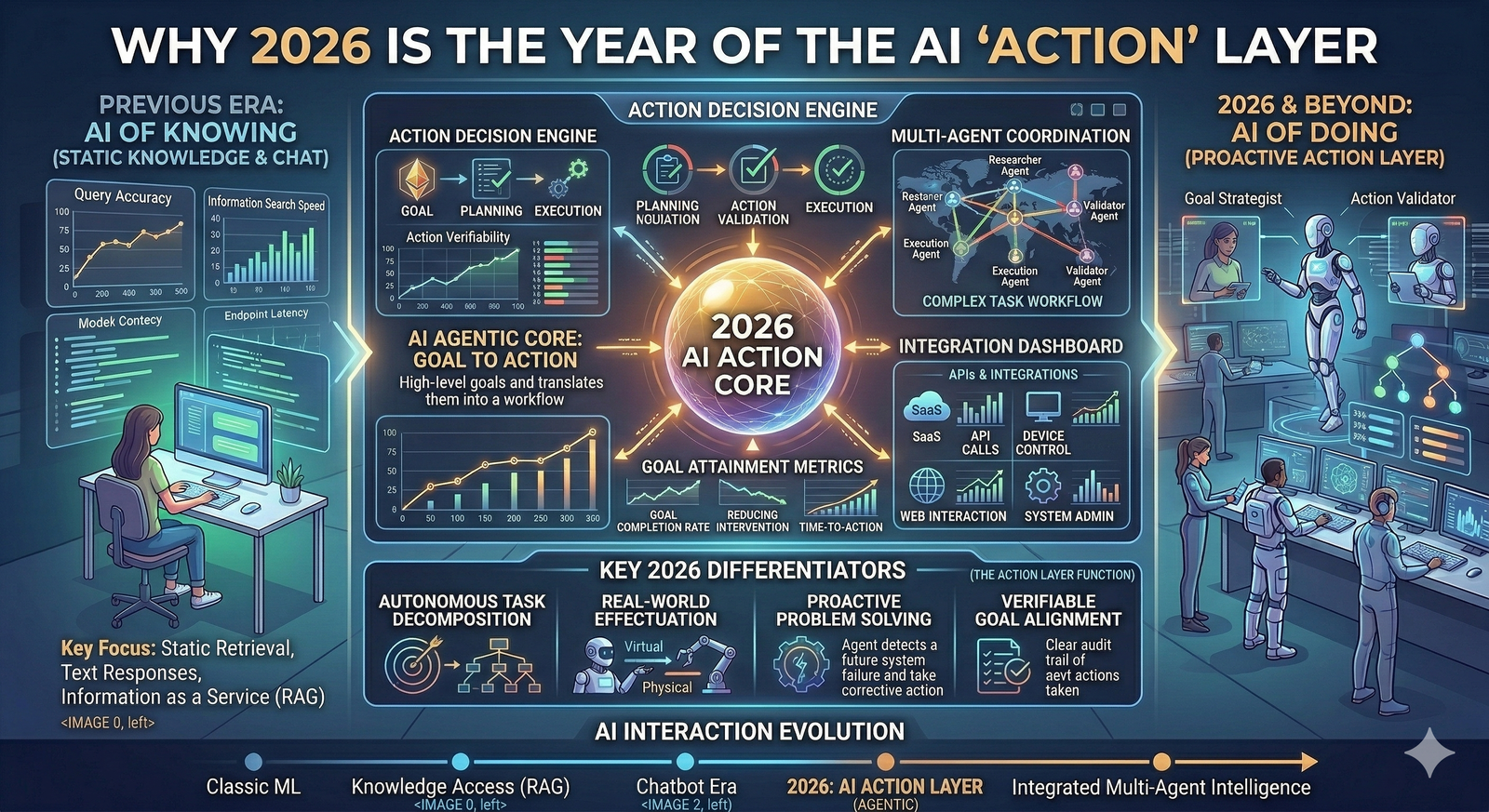
Why 2026 is the Inflection Point
The "AI Arms Race" is in full swing. Attackers are using Agentic AI to conduct vulnerability scans at machine speed. Without an AI-powered Zero Trust backbone, human security teams simply cannot react fast enough.
| Feature | Legacy Zero Trust (2023) | AI-Driven Zero Trust (2026) |
| Authentication | One-time (MFA/SSO) | Continuous (Behavioral/Contextual) |
| Privileges | Static Roles | Dynamic (JIT/JEA) |
| Response | Alert-driven (Human) | Autonomous (AI-led Containment) |
| Scope | Human Users | Humans + AI Agents (NHIs) |
Summary: The "Intelligent" Zero Trust Roadmap
For IT leaders in Wah Cantt and globally, the message is clear: Zero Trust without AI is just a static policy. In 2026, your security must be as autonomous and adaptive as the threats it faces.
 (1).png)