Gemini said
Dunya ab 2026 mein hai, jahan internet ka taqreeban 90% infrastructure open-source software (OSS) par khara hai. Android phones se le kar NASA ke rover tak, har jagah open-source code istemal ho raha hai. Lekin, kya ye "khula" hona waqai ek sahulat hai ya hackers ke liye ek rasta?
ChampsPoint ke is blog mein hum dekhein ge ke kyun Open Source Security ek do-dhari talwar (double-edged sword) hai aur 2026 mein is se kaise bacha jaye.
Open Source Kya Hai? (The "Open Kitchen" Concept)
Open-source ka matlab hai aisa software jis ka "Source Code" dunya mein koi bhi dekh sakta hai, copy kar sakta hai aur tabdeel kar sakta hai. Isay ek "Open Kitchen" samjhein jahan koi bhi ja kar recipe check kar sakta hai aur namak-mirch theek kar sakta hai.
1. Pehli Talwar: The Power of Collaboration (Fayde)
Open source ki sab se bari takat iski Community hai.
Crowdsourced Security: Jab hazaron developers ek hi code ko dekhte hain, toh bugs aur kamzoriyan (vulnerabilities) bohat jaldi pakri jati hain. "Linus’s Law" ke mutabiq: "Given enough eyeballs, all bugs are shallow."
Tez Updates: Jaise hi koi naya khatra (threat) samne aata hai, dunya bhar ke developers mil kar uska "Patch" (hal) nikaal dete hain, aksar kisi bari company se bhi zyada tez.
Transparency: Aapko pata hota hai ke software ke andar kya ho raha hai. Koi "Hidden Backdoor" chhupana mushkil hota hai kyunke code sab ke samne hai.
2. Doosri Talwar: The Hidden Risks (Khatraat)
Wahi "Khulapan" jo iski takat hai, wahi iski sab se bari kamzori bhi ban jata hai.
Hackers ka "Manual": Agar aap code dekh sakte hain, toh hacker bhi dekh sakta hai. Wo sukoon se baith kar code mein "Zero-Day" kamzoriyan dhoondta hai jo abhi tak kisi ne notice nahi ki thin.
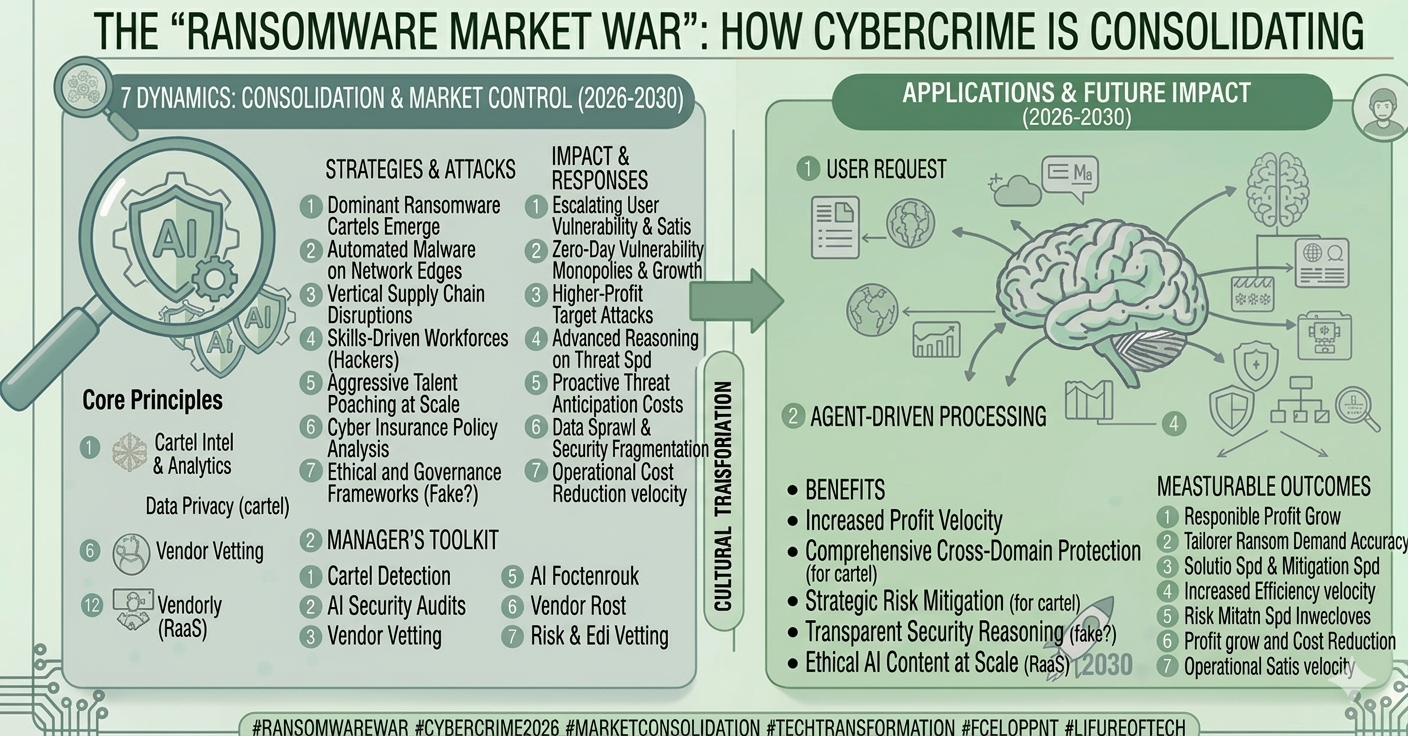
Supply Chain Attacks: 2026 mein ye sab se bara khatra hai. Hackers kisi mashhoor open-source library mein apna "Malicious Code" daal dete hain. Jab hazaron companies us library ko download karti hain, toh wo sab hack ho jati hain (Jaise mashhoor Log4j ya SolarWinds attacks).
Abandonware: Bohat se open-source projects aise hain jinhein banane wala ab unhein update nahi karta. Agar aap aisa purana code use kar rahe hain, toh aap hackers ke liye ek asaan nishana hain.
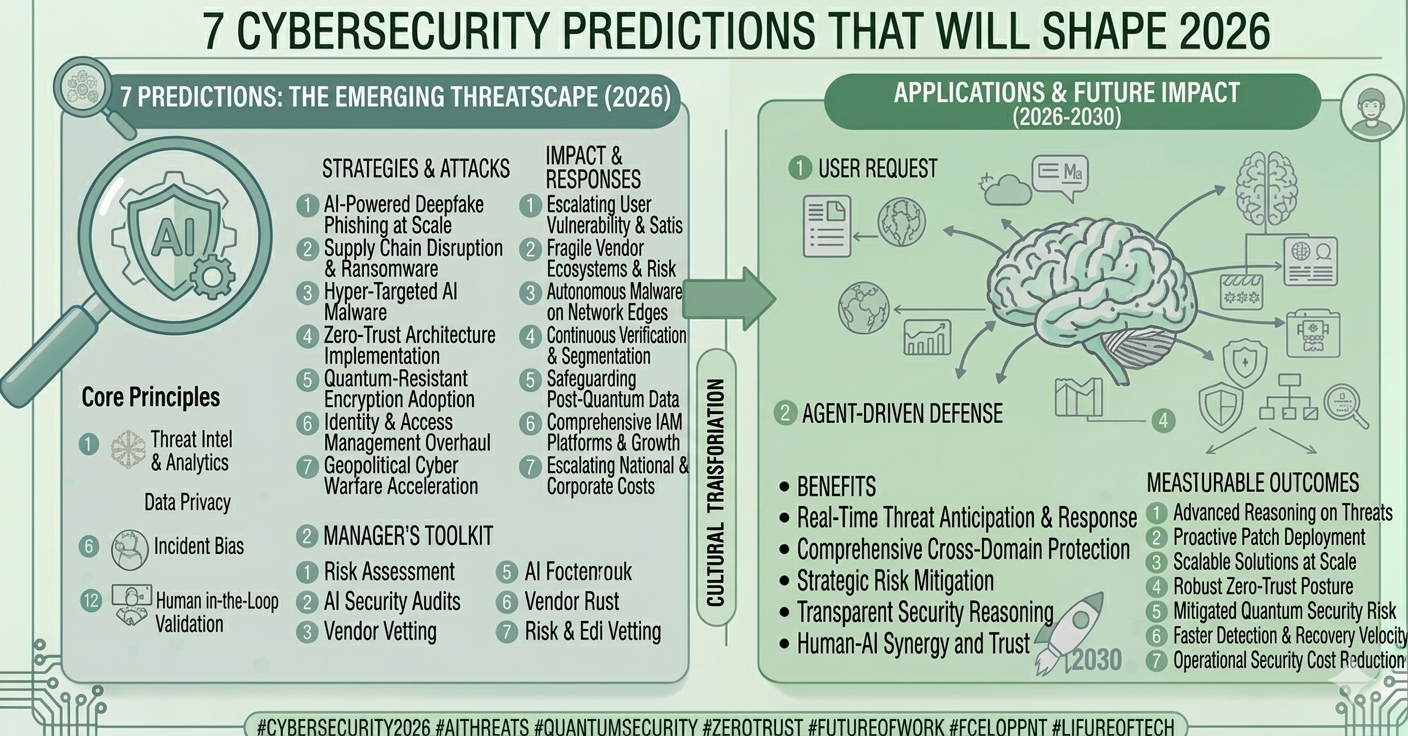
3. 2026 Ka Naya Challenge: AI-Driven Exploits
Ab hackers AI use kar rahe hain jo open-source repositories (jaise GitHub) ko scan karta hai aur seconds mein batata hai ke kis line mein ghalti hai jis se system hack ho sakta hai.
 (1).png)