Zero Trust Architecture: A Simple Explanation for 2026
If you’ve heard the term "Zero Trust" and felt it sounded a bit cynical, you’re actually on the right track. In the world of cybersecurity, trust is a vulnerability. Zero Trust is a framework built on one simple, uncompromising rule: Never trust, always verify.
The Old Way: The "Castle and Moat" Model
For decades, security was like a castle. You built a "moat" (a firewall) and a "drawbridge" (a VPN). Once someone crossed the bridge and entered the castle, they were trusted by default. They could walk into the library, the kitchen, or the vault without being checked again.
The Problem: If a hacker steals just one employee’s password, they are inside the castle. They can move "laterally" to find your most sensitive data, and because they are already "inside," no one stops them.
The New Way: The "Security Guard" Model (Zero Trust)
Zero Trust treats every single person and device as if they are a stranger, even if they are already inside the network. Imagine a high-security building where every door requires a badge swipe, even the door to the bathroom.
The 3 Core Pillars of Zero Trust:
Assume Breach: Zero Trust operates as if a hacker is already in your system. It focuses on limiting how far they can go rather than just trying to keep them out.
Verify Explicitly: Every time you try to access a file or an app, the system checks:
Who are you? (Identity)
What device are you using? (Is it a known phone or a random laptop in another country?)
Where are you? (Is this a weird time of night for you to be working?)
Least Privilege Access: This is the "need-to-know" basis. A graphic designer doesn't need access to the HR payroll files. Zero Trust gives everyone the minimum amount of access they need to do their job—and nothing more.
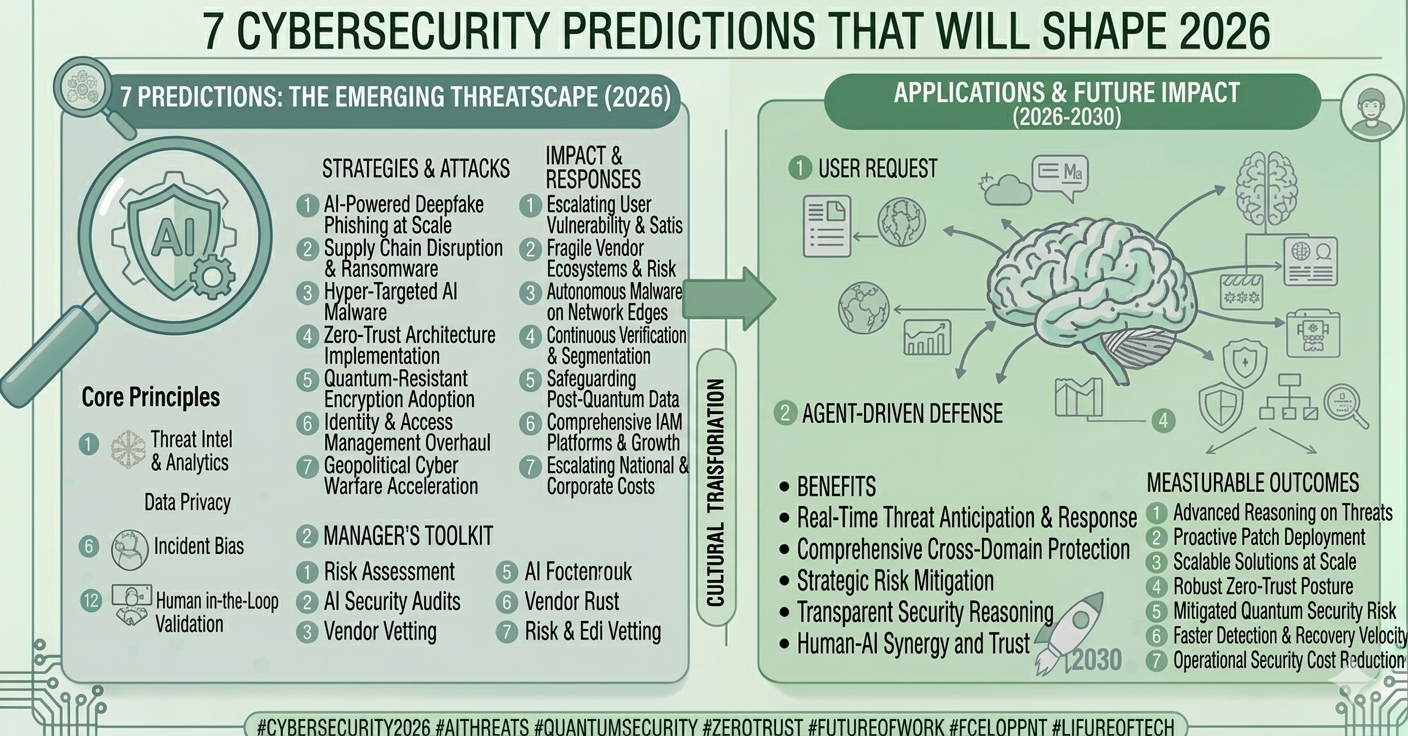
Why is Zero Trust Essential in 2026?
According to recent 2026 reports, 82% of organizations now view Zero Trust as the core of their security strategy. Here’s why it’s winning:
Remote Work Freedom: You don't need a slow, clunky VPN. You can work securely from any Wi-Fi because the security follows you, not the building.
Stops "Lateral Movement": If a hacker gets into one small part of your system, Micro-segmentation (digital internal walls) keeps them trapped there. They can't reach your "crown jewels."
AI-Defense: In 2026, hackers use AI to mimic voices and emails. Zero Trust uses its own AI to spot "anomalies"—like if you suddenly try to download 1,000 files at 2:00 AM—and shuts down access automatically.
Conclusion: Trust is Not a Strategy
Zero Trust isn't about not trusting your employees; it's about protecting them. By removing "implicit trust," we remove the easiest path for hackers to follow. In 2026, Zero Trust is no longer a luxury—it’s the only way to stay safe in a borderless digital world.
 (1).png)