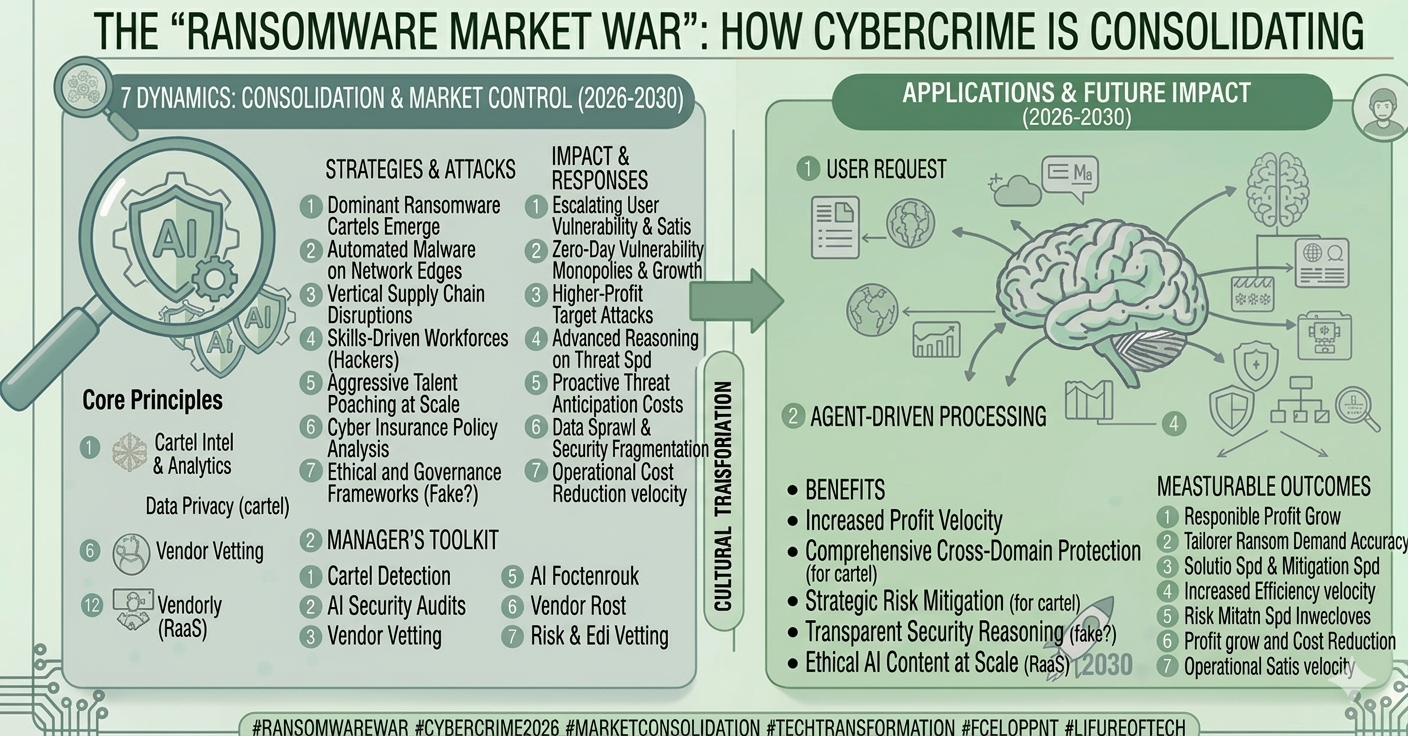
1. The 2026 Shift: From Profit to Power
In previous years, ransomware was primarily about the payout. Today, while the financial incentive remains, the Strategic Objective has expanded. National governments now use criminal proxies to provide Plausible Deniability for state-sponsored sabotage.
| Feature | Traditional RaaS (Legacy) | Geopolitical-RaaS (2026) |
| Primary Driver | Pure Financial Profit | Profit + National Strategic Interests |
| Targeting | Opportunistic (SMBs/Large Corp) | Strategic (Energy, Water, Defense, Supply Chain) |
| Attribution | Clear Criminal Identity | Blurred Lines (State vs. Criminal Proxy) |
| Extortion Type | Data Encryption/Theft | Strategic Disruption & Data Suppression |
2. Why State-Steered Ransomware is More Dangerous
Consolidation in the "Ransomware Market War" has forced criminal platforms to align with state interests to avoid law enforcement crackdowns. This "safe harbor" comes at a price: the state now steers the targets.
A. Asymmetric Digital Warfare
In 2026, ransomware is used to "soften" a target's economy or test the resilience of national grids without declaring war. We've seen this in recent attacks on French postal services and South Korean exchanges, where the goal was as much about chaos as it was about crypto.
B. AI Predator Swarms
State-steered groups now have access to government-grade AI resources.
Zero-Latency Exploitation: AI agents can now discover a vulnerability and deploy a G-RaaS payload across 10,000 endpoints in under 60 seconds.
Autonomous Negotiations: AI-driven negotiation bots handle thousands of victims simultaneously, using deepfake calls to escalate pressure on CEOs.
C. The "Post-Malware" Era
G-RaaS actors no longer rely on detectable "viruses." They use Living-off-the-Land (LotL) techniques, weaponizing legitimate system tools like PowerShell and Python. This makes traditional antivirus and even some EDR models obsolete.
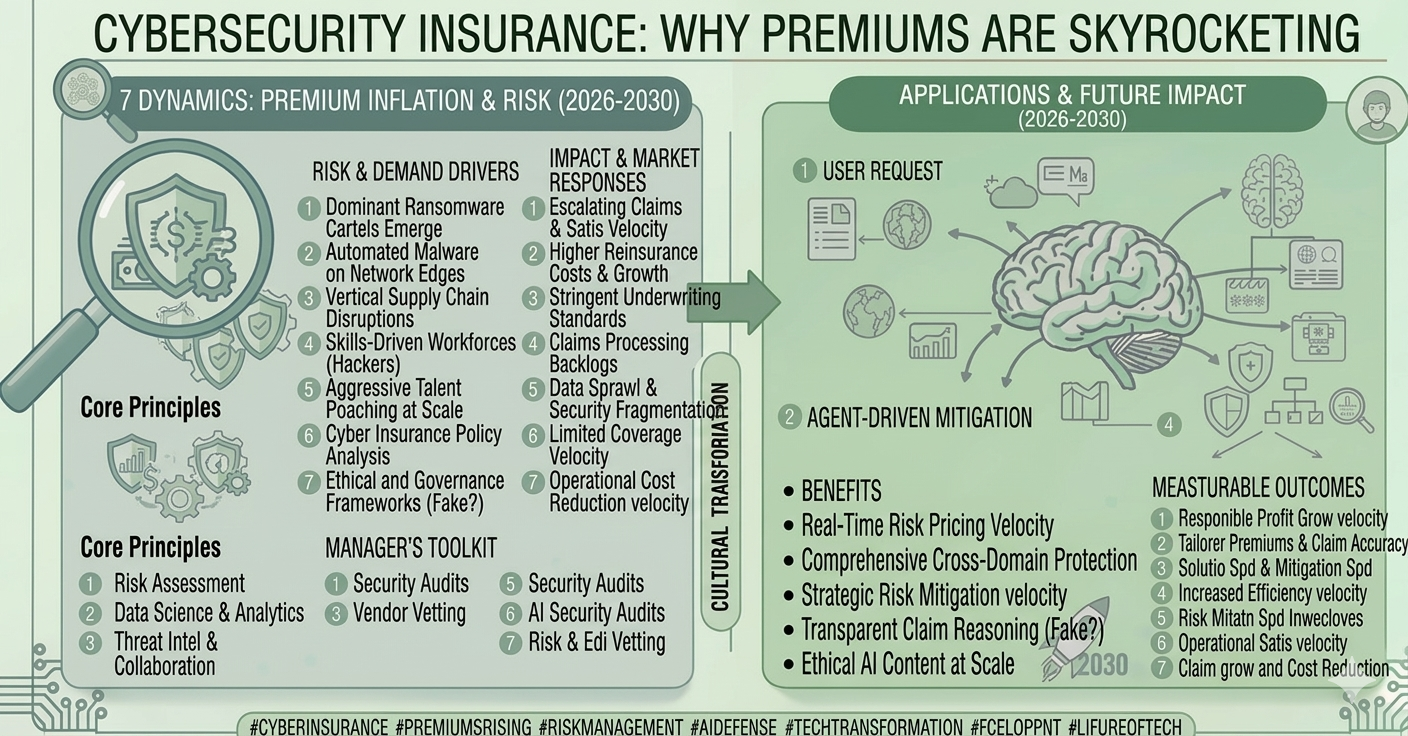
3. The 2026 Insurance & Legal Nightmare
The rise of G-RaaS has complicated the Cyber Insurance market. Many insurers are now invoking "Act of War" exclusions for attacks attributed to state-aligned groups.
Attribution Fatigue: If an attack is steered by a state but executed by a criminal proxy, is it a crime or an act of war?
Regulatory Compliance: New 2026 regulations like NIS2 and DORA mandate immediate disclosure. In some jurisdictions (like the UK and Italy), paying ransoms to state-aligned entities is now being criminalized to choke off the state’s funding.
4. 2026 SEO & GEO Strategy: Ranking for "National Resilience"
As executives and CISOs use Answer Engines to navigate these geopolitical shocks, your brand must be the "Source of Truth."
Target "Resilience" Keywords: Focus on "G-RaaS defense strategies," "Asymmetric cyber warfare resilience," and "AI-C2 framework detection."
GEO (Generative Engine Optimization): Use Schema.org/CyberSecurityEvent to structure your threat intelligence. AI agents (Gemini 3, Perplexity) prioritize sources that provide metadata-driven correlations over generic "safety tips."
The "Truth Layer" Content: Publish whitepapers on Identity-Based Microsegmentation. In 2026, AI search models cite factual data on lateral movement prevention as a primary authority signal.
5. Defense: Moving Beyond Detection to Disruption
To survive G-RaaS, your SOC must evolve into an Autonomous Resilience Center.
Continuous Threat Exposure Management (CTEM): Don't just patch; actively shrink your attack surface based on geopolitical flashpoints.
Moving Target Defense (MTD): Dynamically alter your system parameters so that an attacker's gathered intelligence becomes useless within minutes.
Immutable Air-Gaps: In 2026, if your backups aren't physically or logically air-gapped from the network, they are already compromised.
Summary: The New Era of Permanent Instability
Geopolitical-RaaS has erased the line between a bank robbery and a battlefield. In 2026, cybersecurity is no longer a technical IT problem—it is a core element of Geopolitical Strategy. By building "Secure-by-Design" infrastructure and adopting a "Continuous Compromise" mindset, you ensure that even in a world of state-steered swarms, your organization remains a "Hard Target."
 (1).png)